Windows 10 Pro End of Support Reminder & Windows 11 Qualification for Select GeneXpert Dx Systems
Updated July 17, 2025
As part of Cepheid’s commitment to consistent Microsoft operating system (OS) security patch management, we are reminding you that Microsoft plans to end support for Windows 10 Pro OS on October 14, 2025. After this date, Microsoft will no longer provide critical security patches or updates for Windows 10 Pro OS. To maintain the highest standards of security and performance, we strongly recommend an operating system upgrade on your GeneXpert system.
Cepheid has now qualified an upgrade to Windows 11 Pro OS for select previously shipped GeneXpert Dx systems already running Windows 10 Pro OS (and not running Windows 10 IoT Enterprise LTSC). To be eligible for this upgrade, GeneXpert systems must run GeneXpert Dx software version 6.4 or higher and meet specific computer hardware and operating system requirements
A multi-language flyer (Part Number 303-5234) containing a list of requirements and further information about the Windows 11 Pro OS upgrade option is available. If you have any questions or concerns, please contact Cepheid Technical Support.
CEPHEID PRODUCTS AFFECTED
The following GeneXpert systems are affected:
• GeneXpert Infinity computers running Windows 10 Pro OS
• GeneXpert-II running Windows 10 Pro OS
• GeneXpert-IV running Windows 10 Pro OS
• GeneXpert-XVI running Windows 10 Pro OS
The following GeneXpert systems are not in the scope:
• GeneXpert Infinity and Dx systems running Windows 10 IoT Enterprise LTSC do not require a change as they are still fully supported by Microsoft through ongoing security updates.
• GeneXpert Dx systems connected to a touchscreen do not require a change.
• GeneXpert Xpress Hub systems employed in CLIA-waived environments will continue to receive Windows OS updates until January 9, 2029.
Critical Vulnerability Notification: CVE-2024-38255, CVE-2024-43459, CVE-2024-43462, CVE-2024-48993 through CVE-2024-49018
Updated July 17, 2025
BACKGROUND
The GeneXpert Dx system running Dx 6.5 software is affected by multiple critical vulnerabilities in Microsoft SQL Server 2019 (version 15.0.4223.1), which may allow remote code execution and unauthorized command execution.
For more information, please reference the following: https://support.microsoft.com/enus/topic/kb5046860-description-of-the-security-update-for-sql-server-2019-cu29november-12-2024-4bddde28-482c-4628-a6e2-2d4f542088b7.
CEPHEID PRODUCTS AFFECTED
Dx customers using GeneXpert Dx 6.5 software are impacted.
ACTIONS REQUIRED BY CUSTOMERS
1. Verify Current SQL Server Version
Navigate to the following path and check the version:
C:\Program Files\Microsoft SQL
Server\MSSQL15.MSSQLSERVER\MSSQL\Binn\sqlservr.exe If the version is 15.0.4223.1, proceed to the next step.
2. Download and Apply Patch
Double-click on the link below to for the executable to install:
https://catalog.s.download.windowsupdate.com/d/msdownload/update/software/s ecu/2024/11/sqlserver2019-kb5046860-
x64_618ad2ed38cad99be8fc5688ab98a10813e98de1.exe
3. Verify Update
After installation, confirm that the SQL Server version is updated to 15.0.4410.1.
Adobe Reader Update & Critical Vulnerability Notification: CVE-2024-49530 through CVE-2024-49535 & CVE-2025-24431, CVE-2025-27158 through CVE-2025-27164, CVE2025-27174
Updated July 17, 2025
BACKGROUND
Multiple vulnerabilities have been identified in Adobe Acrobat Reader versions prior to 25.001.20432, which may allow arbitrary code execution. These are documented under APSB25-14.
CEPHEID PRODUCTS AFFECTED
Dx customers using GeneXpert Dx 6.5 software are impacted.
GeneXpert Xpress customers using GeneXpert Xpress 6.4a software are impacted.
ACTIONS REQUIRED BY CUSTOMERS
1. Verify Installed Version
Path: C:\Program Files (x86)\Adobe\Acrobat Reader DC\Reader If the version is below 25.001.20432, proceed to the next step.
2. Download and Install Update
Visit Adobe Acrobat Reader Download Page
- Click on “More download options” and install version 25.001.20432 (preferred)
- If this version is not available, upgrade to version 24.005.20320
3. Verify Update
Confirm that the version is updated to 25.001.20432 or 24.005.20320
Critical Vulnerability Notification: Windows 10 Security Update KB5049981
Updated July 17, 2025
BACKGROUND
The remote Windows 10 host is missing security update KB5049981, exposing it to potential vulnerabilities including privilege escalation and remote code execution.
For more information, please reference the following: https://support.microsoft.com/enus/topic/january-14-2025-kb5049981-os-builds-19044-5371-and-19045-5371-12f3788f6e7d-4524-8ab3-27d1666e0510
The following CVEs are in scope: CVE-2024-7344, CVE-2025-21189, CVE-2025-21202,
CVE-2025-21207, CVE-2025-21210-21211, CVE-2025-21213-21215, CVE-2025-21217,
CVE-2025-21219-21220, CVE-2025-21223-21224, CVE-2025-21226-21246, CVE-202521248-21252, CVE-2025-21255-21258, CVE-2025-21260-21261, CVE-2025-21263, CVE2025-21265-21266, CVE-2025-21268-21278, CVE-2025-21280-21282, CVE-2025-21284-
21296, CVE-2025-21298-21308, CVE-2025-21310, CVE-2025-21312, CVE-2025-21314,
CVE-2025-21316-21321, CVE-2025-21323-21324, CVE-2025-21327-21336, CVE-202521338-21341, CVE-2025-21374, CVE-2025-21378, CVE-2025-21382, CVE-2025-21389,
CVE-2025-21409, CVE-2025-21411, CVE-2025-21413, CVE-2025-21417
CEPHEID PRODUCTS AFFECTED
Dx customers using GeneXpert Dx 6.5 software running Windows 10 version 21H2 or 22H2 are impacted.
ACTIONS REQUIRED BY CUSTOMERS
1. Download and Apply Path
Double-click the .msu file to install:
https://catalog.s.download.windowsupdate.com/d/msdownload/update/software/s ecu/2025/01/windows10.0-kb5049981-
x64_bda073f7d8e14e65c2632b47278924b8a0f6b374.msu
2. Verify Update
Confirm that the system has been updated via Windows Update history or system info.
Critical Vulnerability Notification: CVE-2025-21176
Updated July 17, 2025
BACKGROUND
The Microsoft .NET Framework 4.8.1 installation on the remote host is missing a security update exposing it to remote code execution. This vulnerability may allow attackers to execute unauthorized code via a specially crafted request.
For more information, please reference the following: https://support.microsoft.com/enus/topic/january-14-2025-kb5049621-cumulative-update-for-net-framework-3-5-and-4-81-for-windows-10-version-21h2-and-windows-10-version-22h2-3c3adbc9-113c-410897d2-cdbedfee776f.
CEPHEID PRODUCTS AFFECTED
Dx 6.5 systems running Microsoft .NET Framework 4.8.1 are impacted.
ACTIONS REQUIRED BY CUSTOMERS
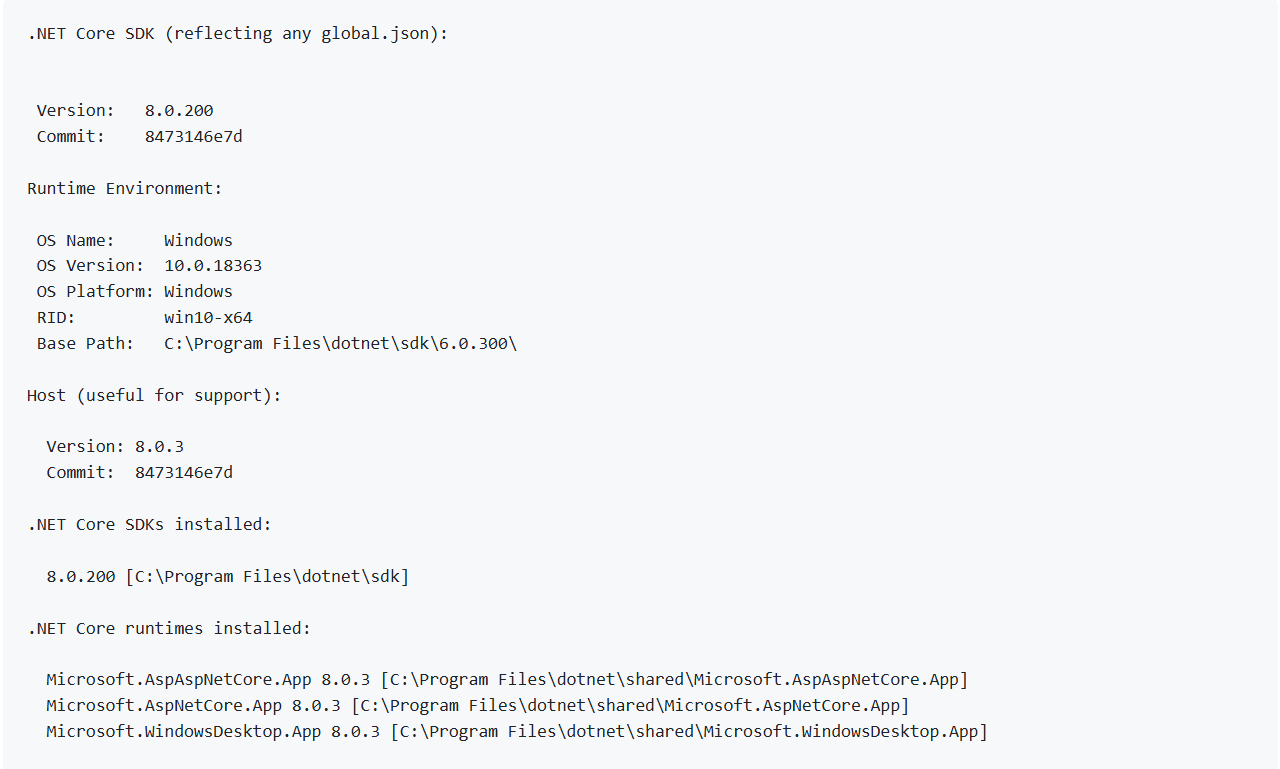
1. Verify Current Version Navigate to:
C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorlib.dll
- If the version is 4.8.9256.0, proceed to the next step.
2. Download and Apply Patch
Double-click on the .msu file to install:
https://catalog.s.download.windowsupdate.com/d/msdownload/update/software/s ecu/2024/12/windows10.0-kb5049621-x64-
ndp481_8cf3ab9195ec940d2da51894fb690b2d21404e8e.msu
3. Verify Update
Confirm that the version is updated to 4.8.9290.0.
TLS 1.0/1.1 Protocol Support
Updated July 17, 2025
BACKGROUND
The remote service accepts connections encrypted using TLS 1.0 and TLS 1.1, which are outdated and insecure protocols. These protocols are potentially vulnerable to multiple cryptographic attacks and should be disabled in favor of TLS 1.2 or TLS 1.3.
For more information, please reference the following:
• https://www.tenable.com/plugins/nessus/104743
• https://www.tenable.com/plugins/was/112546
CEPHEID PRODUCTS AFFECTED
GeneXpert Xpress customers using GeneXpert Xpress 6.4a software are impacted.
ACTIONS REQUIRED BY CUSTOMERS
Before updating the Windows registry file, Cepheid strongly recommends that you work with your IT group or representative to ensure the update is performed in a manner that does not affect the functioning of the system. If you have any questions or concerns, please contact Cepheid Technical Support.
Cepheid highly recommends backing up the registry and test result data or the database. For instructions on how to shut down the software and back up test result data, please consult the user manual.
Once back up of the registry and database or test data is complete, proceed with the following:
Steps to follow to apply this.
1. Search for "Registry Editor" in windows search bar.
2. Navigate to below path.
Computer\HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders \SCHANNEL\Protocols
3. Under Protocols create two keys (folders) structure for TLS 1.0 and TLS 1.1 Note: Right click on the Protocols to create a new key.
4. Under each TLS folders create two more keys (folders) as Client and Server
5. Click on the client folder, on the RHS empty space right click and select NEW-DWORD option.
6. Rename to "Enabled" and should have the value set to "0"
Note: Same values to be created for TLS 1.0 and TLS 1.1 and both client and server folders.
7. Close the editor.
8. Open SQL Server configuration manager.
9. Click on SQL Server Services option.
10. Stop and start the SQL Server (MSSQLSERVER) service.
11. Close the SQL server configuration manager application.
12. Download Nmap tool from Google and install it in the system.
13. Open command prompt and enter the below command.
nmap -script ssl-enum-ciphers -p 1433 localhost
14. Hit the Enter button on the keyboard.
15. Verify that only TLS 1.2 and above is displayed in the cmd prompt.
Critical Vulnerability Notification: Microsoft SQL Server 2017
Updated July 17, 2025
BACKGROUND
The Microsoft SQL Server 2017 installation on the remote host is missing security update KB5046858, exposing it to potential remote code execution vulnerabilities.
For more information, please reference the following: https://support.microsoft.com/enus/topic/kb5046858-description-of-the-security-update-for-sql-server-2017-cu31november-12-2024-2984d3a5-0683-4f9b-9e6a-3888e67bd859.
The following CVEs are in scope: CVE-2024-38255, CVE-2024-43459, CVE-2024-43462, CVE-2024-48993 through CVE-2024-49043
CEPHEID PRODUCTS AFFECTED
GeneXpert Xpress customers using GeneXpert Xpress 6.4a software are impacted.
ACTIONS REQUIRED BY CUSTOMERS
1. Verify Current SQL Server Version Path:
C:\Program Files\Microsoft SQL
Server\MSSQL14.MSSQLSERVER\MSSQL\Binn\sqlservr.exe
- If the version is 14.0.3294.2, proceed to the next step.
2. Download and Apply Patch
Double-click on the executable file link here:
https://catalog.s.download.windowsupdate.com/c/msdownload/update/software/s ecu/2024/11/sqlserver2017-kb5046858-
x64_b681ef619a79265439b4109c01a02f54cfe89928.exe
3. Verify Update
Confirm that the version is updated to 14.0.3485.1.
Critical Vulnerability Notification: Windows 10 Security Update KB5051974, KB505518, KB5060633
Updated July 17, 2025
BACKGROUND
The remote Windows 10 host is missing security update KB5051974, which addresses multiple vulnerabilities including remote code execution and privilege escalation.
The following CVEs are in scope: CVE-2025-21181, CVE-2025-21184, CVE-2025-21190,
CVE-2025-21200, CVE-2025-21201, CVE-2025-21212, CVE-2025-21216, CVE-2025-21254,
CVE-2025-21337, CVE-2025-21347, CVE-2025-21349 through CVE-2025-21420
CEPHEID PRODUCTS AFFECTED
Dx customers using GeneXpert Dx 6.5 software are impacted.
ACTIONS REQUIRED BY CUSTOMERS
1. Download and Apply Patch
Double-click the .msu file to install:
https://catalog.s.download.windowsupdate.com/c/msdownload/update/software/s ecu/2025/02/windows10.0-kb5051974-
x64_74aa601c3966a9e1ad4efe6287550c0f0bdea59d.msu
2. Verify Update for KB5051974
Confirm installation via Windows Update history or system info.
3. Additional Updates for KB5055518 & KB5060533
Please proceed with the latest Microsoft Windows Security Update which would allow your system to be fully protected from this vulnerability. Customers with automatic updates do not need to take further action. If you have not yet automated Windows updates, select Start > Settings > Update & Security > Windows Update and then select ‘Check for updates’.
Critical Vulnerability Notification: Windows 10 Security Update KB5060533
Updated July 17, 2025
BACKGROUND
The remote Windows 10 host is missing security update KB5060533. This update addresses vulnerabilities in the Windows kernel that could allow privilege escalation and denial of service.
The following CVEs are in scope: CVE-2024-9157, CVE-2025-21180, CVE-2025-21247,
CVE-2025-24035, CVE-2025-24044, CVE-2025-24046, CVE-2025-24048, CVE-2025-24050–
24051, CVE-2025-24054–24056, CVE-2025-24059, CVE-2025-24061, CVE-2025-24066– 24067, CVE-2025-24071–24072, CVE-2025-24984–24985, CVE-2025-24987–24988, CVE-
2025-24991–24993, CVE-2025-24995–24997, CVE-2025-26633, CVE-2025-26645
CEPHEID PRODUCTS AFFECTED
Dx customers using GeneXpert Dx 6.5 software are impacted.
ACTIONS REQUIRED BY CUSTOMERS
1. Verify Current Kernel Version
Path: C:\Windows\system32\ntoskrnl.exe
- If the version is 10.0.19041.4894, proceed to the next step.
2. Download and Apply Patch Download KB5060533 -
https://www.catalog.update.microsoft.com/Search.aspx?q=KB5060533%20windo ws%2010%20x64
3. Verify Update
After applying the patch, confirm that the kernel version is updated to 10.0.19041.5965.
Note: This is a cumulative update. Applying KB5060533 alone is sufficient and includes all prior kernel-level security fixes.
Critical Vulnerability Notification: Windows 10 Security Update KB5060533
Updated July 17, 2025
BACKGROUND
The remote Windows 10 host is missing security update KB5060533, which addresses critical vulnerabilities in the Windows kernel and system components.
For more information, please reference the following: https://support.microsoft.com/enus/topic/june-10-2025-kb5060533-os-builds-19044-5965-and-19045-5965-eeae388cca1c-4569-95d7-3d7be2e0b8ba
The following CVEs are in scope: CVE-2025-21191, CVE-2025-21197, CVE-2025-21204,
CVE-2025-21205, CVE-2025-21221, CVE-2025-21222, CVE-2025-24058, CVE-2025-24060, CVE-2025-24062, CVE-2025-24073, CVE-2025-24074, CVE-2025-26635, CVE-2025-26637,
CVE-2025-26639, CVE-2025-26640, CVE-2025-26641, CVE-2025-26644, CVE-2025-26648,
CVE-2025-26663, CVE-2025-26665, CVE-2025-26666, CVE-2025-26668, CVE-2025-26669,
CVE-2025-26670, CVE-2025-26672, CVE-2025-26673, CVE-2025-26674, CVE-2025-26675,
CVE-2025-26678, CVE-2025-26679, CVE-2025-26681, CVE-2025-26686, CVE-2025-26687,
CVE-2025-26688, CVE-2025-27467, CVE-2025-27469, CVE-2025-27471, CVE-2025-27473,
CVE-2025-27476, CVE-2025-27477, CVE-2025-27478, CVE-2025-27481, CVE-2025-27484,
CVE-2025-27487, CVE-2025-27490, CVE-2025-27491, CVE-2025-27727, CVE-2025-27729,
CVE-2025-27730, CVE-2025-27731, CVE-2025-27732, CVE-2025-27735, CVE-2025-27736,
CVE-2025-27737, CVE-2025-27738, CVE-2025-27739, CVE-2025-27742, CVE-2025-29809, CVE-2025-29810, CVE-2025-29824.
CEPHEID PRODUCTS AFFECTED
Dx customers using GeneXpert Dx 6.5 software are impacted.
ACTIONS REQUIRED BY CUSTOMERS
1. Verify Current Kernel Version
Path: C:\Windows\system32\ntoskrnl.exe
- If the version is 10.0.19041.5369, proceed to the next step.
2. Download and Apply Patch
Download KB5060533 for 2025-04 Cumulative Update for Windows 10 Version 22H2 for x64-based Systems (the first row listed here):
https://www.catalog.update.microsoft.com/Search.aspx?q=KB5060533%20windo ws%2010%20x64
3. Verify Update
Confirm that the kernel version is updated to 10.0.19041.5965.